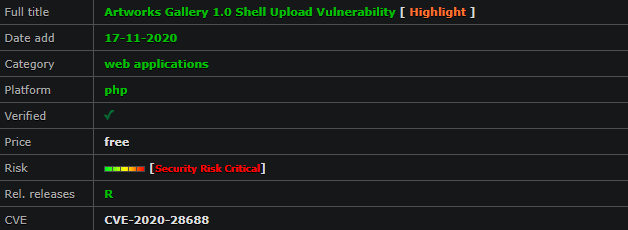
artwotrkvuln
Artworks Gallery Exploit – Arbitrary File Upload – RCE (Authenticated)
[Security Risk Critical] [PHP Web Apps]
The add artwork functionality in ARTWORKS GALLERY IN PHP, CSS, JAVASCRIPT, AND MYSQL 1.0 allows remote attackers to upload arbitrary files.
*Artworks Gallery - Arbitrary File Upload - RCE (Authenticated) - Edit
Profile*
# Exploit Title: Artworks Gallery - Arbitrary File Upload - RCE
(Authenticated) - Edit Profile
# Date: November 17th, 2020
# Exploit Author: Shahrukh Iqbal Mirza (@shahrukhiqbal24)
# Vendor Homepage: Source Code & Projects (https://code-projects.org)
# Software Link: ARTWORKS GALLERY IN PHP, CSS, JAVASCRIPT, AND MYSQL (
https://download.code-projects.org/details/9dfede24-03cc-42a8-b319-f666757ac7cf
)
# Version: 1.0
# Tested On: Windows 10 (XAMPP Server)
# CVE: CVE-2020-28687
-----------------------------------------------------------------------------------------------------------
*Proof of Concept:*
-----------------------------------------------------------------------------------------------------------
1. Authenticate as a user (or signup as an artist)
2. Go to edit profile
3. Upload a php-shell as profile picture and click update/save
4. Find your shell at 'http://<ip>/<base_url>/pictures/profile/<shell.php>'
and get command execution
----------
*Artworks Gallery - Arbitrary File Upload - RCE (Authenticated) - Add
Artwork*
# Exploit Title: Artworks Gallery - Arbitrary File Upload - RCE
(Authenticated) - Add Artwork
# Date: November 17th, 2020
# Exploit Author: Shahrukh Iqbal Mirza (@shahrukhiqbal24)
# Vendor Homepage: Source Code & Projects (https://code-projects.org)
# Software Link: ARTWORKS GALLERY IN PHP, CSS, JAVASCRIPT, AND MYSQL (
https://download.code-projects.org/details/9dfede24-03cc-42a8-b319-f666757ac7cf
)
# Version: 1.0
# Tested On: Windows 10 (XAMPP Server)
# CVE: CVE-2020-28688
-----------------------------------------------------------------------------------------------------------
Proof of Concept:
-----------------------------------------------------------------------------------------------------------
1. Authenticate as a user (or signup as an artist)
2. Click the drop down for your username and go to My ART+BAY
3. Click on My Artworks > My Available Artworks > Add an Artwork
4. Click on any type of artwork and instead of the picture, upload your
php-shell > click on upload
5. Find your shell at 'http://<ip>/<base_url>/pictures/arts/<shell.php>'
and get command executionWhy not subscribe to our newsletter?
669 total views, 2 views today
Latest posts by RiSec.n0tst3 (see all)