\ Latest Updates
Aggregated InfoSec News
Packetstorm
- Feed has no items.
THN
- Over 70 Malicious npm and VS Code Packages Found...by info@thehackernews.com (The Hacker News) on 26 May 2025 at 3:17 PM
As many as 60 malicious npm packages have been discovered in the package registry with malicious functionality to harvest hostnames, IP addresses, DNS servers, and user directories to a Discord-controlled endpoint. The packages, published under three different accounts, come with an install‑time […]
- CISO's Guide To Web Privacy Validation And Why...by info@thehackernews.com (The Hacker News) on 26 May 2025 at 12:25 PM
Are your web privacy controls protecting your users, or just a box-ticking exercise? This CISO’s guide provides a practical roadmap for continuous web privacy validation that’s aligned with real-world practices. – Download the full guide here. Web Privacy: From Legal Requirement to Business […]
- ⚡ Weekly Recap: APT Campaigns, Browser Hijacks,...by info@thehackernews.com (The Hacker News) on 26 May 2025 at 10:23 AM
Cyber threats don't show up one at a time anymore. They’re layered, planned, and often stay hidden until it’s too late. For cybersecurity teams, the key isn’t just reacting to alerts—it’s spotting early signs of trouble before they become real threats. This update is designed to deliver […]
PortSwigger
- We’re going teetotal: It’s goodbye to The...on 2 March 2023 at 3:05 PM
PortSwigger today announces that The Daily Swig is closing down
- Bug Bounty Radar // The latest bug bounty...on 28 February 2023 at 8:15 PM
New web targets for the discerning hacker
- Indian transport ministry flaws potentially...on 28 February 2023 at 3:15 PM
Armed with personal data fragments, a researcher could also access 185 million citizens’ PII
Security Affaris
- China-linked APT UNC5221 started exploiting...by Pierluigi Paganini on 26 May 2025 at 12:31 PM
China-linked APT exploit Ivanti EPMM flaws to target critical sectors across Europe, North America, and Asia-Pacific, according to EclecticIQ. Researchers from EclecticIQ observed a China-linked APT group that chained two Ivanti EPMM flaws, tracked as CVE-2025-4427 and CVE-2025-4428, in attacks […]
- Fake software activation videos on TikTok spread...by Pierluigi Paganini on 26 May 2025 at 9:12 AM
Crooks use TikTok videos with fake tips to trick users into running commands that install Vidar and StealC malware in ClickFix attacks. Cybercriminals leverage AI-generated TikTok videos in ClickFix attacks to spread Vidar and StealC malware, reports Trend Micro. These videos trick users into […]
- SECURITY AFFAIRS MALWARE NEWSLETTER ROUND 46by Pierluigi Paganini on 25 May 2025 at 2:30 PM
Security Affairs Malware newsletter includes a collection of the best articles and research on malware in the international landscape Sarcoma Ransomware Unveiled: Anatomy of a Double Extortion Gang RVTools Bumblebee Malware Attack – How a Trusted IT Tool Became a Malware Delivery Vector […]
HackerOne
- Feed has no items.
WeLiveSecurity
- Danabot under the microscopeon 23 May 2025 at 12:43 PM
ESET Research has been tracking Danabot’s activity since 2018 as part of a global effort that resulted in a major disruption of the malware’s infrastructure
- Danabot: Analyzing a fallen empireon 22 May 2025 at 9:03 PM
ESET Research shares its findings on the workings of Danabot, an infostealer recently disrupted in a multinational law enforcement operation
- Lumma Stealer: Down for the counton 22 May 2025 at 3:53 PM
The bustling cybercrime enterprise has been dealt a significant blow in a global operation that relied on the expertise of ESET and other technology companies
TheRegister
- Cybercrime is 'orders of magnitude' larger than...by Jessica Lyons on 24 May 2025 at 6:47 PM
Michael Daniel also thinks Uncle Sam should increase help to orgs hit by ransomware INTERVIEW Uncle Sam's cybersecurity apparatus can't only focus on China and other nation-state actors, but also has to fight the much bigger damage from plain old cybercrime, says former White House advisor […]
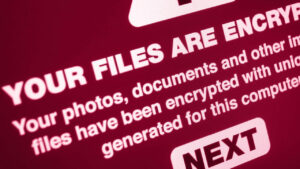
- Ransomware scum leaked Nova Scotia Power...by Jessica Lyons on 23 May 2025 at 6:45 PM
Bank accounts, personal details all hoovered up in the attack Nova Scotia Power on Friday confirmed it had been hit by a ransomware attack that began earlier this spring and disrupted certain IT systems, and admitted the crooks leaked data belonging to about 280,000 customers online. The stolen […]
- Suspected creeps behind DanaBot malware that hit...by Iain Thomson on 23 May 2025 at 2:31 AM
And the associated fraud'n'spy botnet is about to be shut down The US Department of Justice has unsealed indictments against 16 people accused of spreading and using the DanaBot remote-control malware that infected more than 300,000 computers, plus operating a botnet of the same name, and appears […]
Security Week
- Nova Scotia Power Confirms Ransomware Attack,...by Eduard Kovacs on 26 May 2025 at 7:43 AM
Nova Scotia Power has finally admitted that the recent cyberattack was a ransomware attack, but it hasn’t paid the hackers. The post Nova Scotia Power Confirms Ransomware Attack, 280k Notified of Data Breach appeared first on SecurityWeek.
- Signal Adds Screenshot-Blocker to Thwart...by Ryan Naraine on 23 May 2025 at 3:13 PM
Signal said the privacy feature is on by default for every Windows 11 user to block Microsoft from taking screenshots for Windows Recall. The post Signal Adds Screenshot-Blocker to Thwart ‘Windows Recall’ appeared first on SecurityWeek.
- In Other News: Volkswagen App Hacked, DR32...by SecurityWeek News on 23 May 2025 at 2:41 PM
Noteworthy stories that might have slipped under the radar: serious vulnerabilities found in a Volkswagen app, Australian hacker DR32 sentenced in the US, and Immersive launches OT security training solution. The post In Other News: Volkswagen App Hacked, DR32 Sentenced, New OT Security Solution […]
Exploit-DB Updates
- [local] Microsoft Windows Server 2016 - Win32k...on 25 May 2025 at 1:00 AM
Microsoft Windows Server 2016 - Win32k Elevation of Privilege
- [webapps] WordPress User Registration &...on 25 May 2025 at 1:00 AM
WordPress User Registration & Membership Plugin 4.1.2 - Authentication Bypass
- [remote] Grandstream GSD3710 1.0.11.13 - Stack...on 25 May 2025 at 1:00 AM
Grandstream GSD3710 1.0.11.13 - Stack Buffer Overflow
- [webapps] Java-springboot-codebase 1.1 -...on 25 May 2025 at 1:00 AM
Java-springboot-codebase 1.1 - Arbitrary File Read
- [remote] Windows 2024.15 - Unauthenticated...on 25 May 2025 at 1:00 AM
Windows 2024.15 - Unauthenticated Desktop Screenshot Capture
- [remote] ABB Cylon Aspect 3.08.03 - Guest2Root...on 25 May 2025 at 1:00 AM
ABB Cylon Aspect 3.08.03 - Guest2Root Privilege Escalation