Portuguese newspaper Expresso hacked by attackers at dawn this Sunday, 2nd January 2022.
Those responsible for the invasion are the Lapsus Group, the same team that shut down the Ministry of Health’s systems last December.
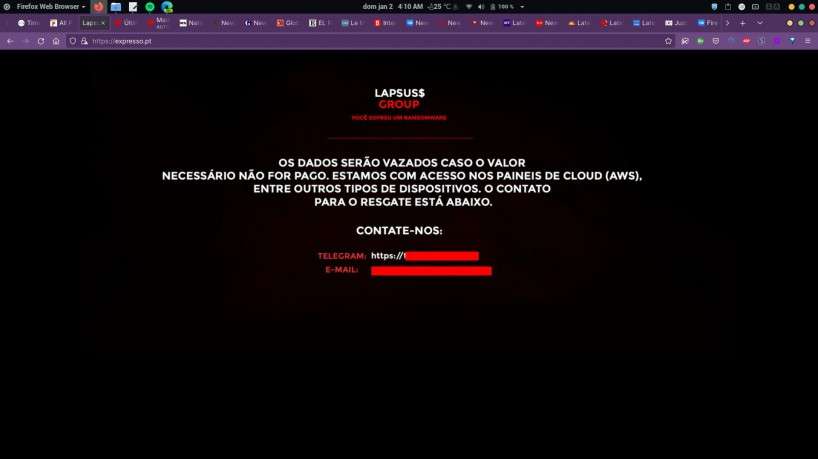
The newspaper’s website displays a page similar to the one shown in the attack on the Brazilian government agency. hackers announced that they will leak data if they do not receive a value, and said they have control of the portal’s hosting system.
In addition to the website, hackers from the Lapsus Group hacked the newspaper Expresso’s Twitter profile.
“Lapsus$ is officially the new president of Portugal”
Expresso’s Twitter profile
Social networks in the newspaper such as Instagram and Facebook, are unaffected.
About the newspaper hack
Group that invaded newspaper Expresso also attacked Ministry of Health in December 2021
Last December, the Ministry of Health of Brazil was the subject of an attack by the same attackers. A number of their systems were rendered unavailable at the time.
Lapsus Group claims to have stolen documents from operator Claro
The Lapsus Group also claims authorship of an attack against operator Claro, in the last week of last year. The company’s services, such as customer service channels, recharge of prepaid telephones and in-store systems, were offline between the 27th and 29th of December.
Procon-SP even notified the operator about the failure. The company may be fined up to R$ 11 million. Claro says that the problem was due to “a systemic instability”, and denies that there was an invasion.
Hackers, in turn, published screenshots of the operator’s internal systems, and claim to have had access to 10,000 TB of data. The website Techblog, specializing in technology news, obtained confirmation from Claro employees that the images are legitimate, and that the company had indeed suffered the virtual invasion.