Best security practices are the responsibility of all developers, with the recent surges in fraudulent login attempts, it serves as a good reminder that account security is the pillar to good organizational security practices:
As GitHub’s Staff Security Analyst @sanjuanswan noted during a recent security Twitter space
“your organization is only as secure as your least secure member”
It’s our responsibility to promote good security practices, whether you are an individual contributor or team lead. Here are three steps you can take today to set an effective model of security practices.
1. 🛠 Enable MFA:
Enabling 2FA adds an extra layer of security when logging into your GitHub account. With 2FA, you have to log in with your username and password and provide another form of authentication that only you know or have access to. If you lose access to your selected authentication method, you can use the provided recovery codes to access your account. Don’t forget to download and store those recovery codes somewhere secure.
At the organizational level, owners can require that members, billing managers, and outside collaborators use two-factor authentication to secure their personal accounts. Set this standard at the organizational level.
2. 🔐 Keep your email accounts up to date and safe

GitHub protects your account by requiring you to click a link sent to your email address when you log in from a new device. If a potential attacker doesn’t also have access to your email account, they can’t ATO (account take over) your GitHub account.
Use a unique, and complex password for your email account; the best way to accomplish this is by using a password manager.
Don’t share email addresses or login information with your team, and keep a recurring audit, or even better, add an off-boarding step so departing team members no longer has access to your repos.
3. 📱 Download the GitHub Mobile Application
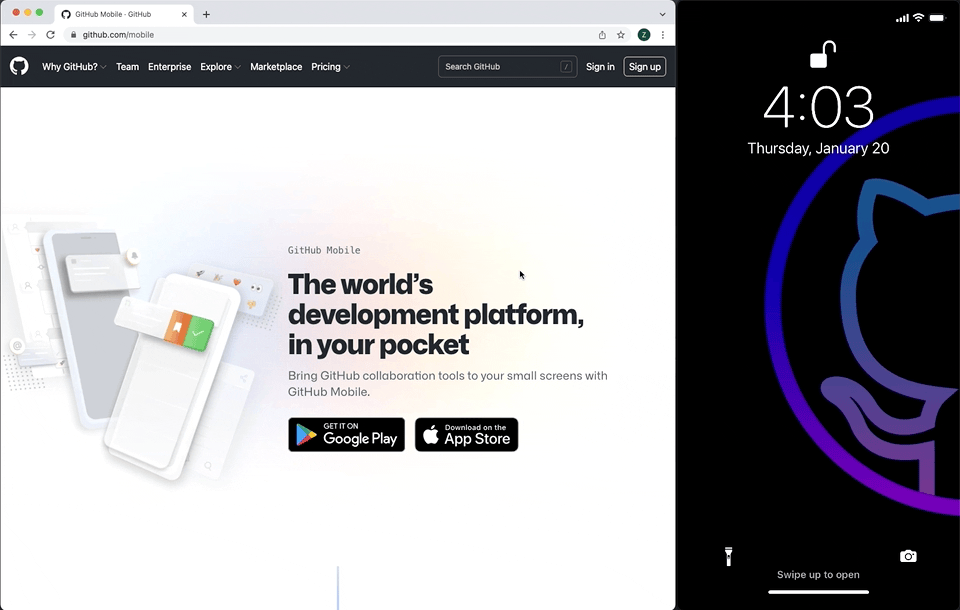
You can use GitHub Mobile for 2FA when logging in to your GitHub account in a web browser. 2FA with GitHub Mobile does not rely on TOTP, and instead uses public-key cryptography to secure your account.
To get started with GitHub mobile for 2FA, if you’re not already using the mobile app, you can install it now and sign in to your account. And if you haven’t set up 2FA, set it up via your account security settings. You’ll need to set up 2FA with SMS or another time-based one-time password (TOTP) app first to start using Mobile 2FA. Once you have configured a TOTP application, or SMS, you can also use GitHub Mobile to authenticate youtube.
Conclusion:
Most software vulnerabilities are mistakes, not malicious attacks. Do your part and secure the software you write today, starting with your GitHub account security.
Stay Safe!
You may also enjoy reading, Q4/21: Sees More DDoS Attacks Than Ever Before
Stay informed of the latest Cybersecurity trends, threats and developments. Sign up for RiSec Weekly Cybersecurity Newsletter Today
Remember, CyberSecurity Starts With You!
- Globally, 30,000 websites are hacked daily.
- 64% of companies worldwide have experienced at least one form of a cyber attack.
- There were 20M breached records in March 2021.
- In 2020, ransomware cases grew by 150%.
- Email is responsible for around 94% of all malware.
- Every 39 seconds, there is a new attack somewhere on the web.
- An average of around 24,000 malicious mobile apps are blocked daily on the internet.




