The FBI released a flash alert containing technical details associated with the LockBit ransomware operation.
The Federal Bureau of Investigation (FBI) has issued a flash alert containing technical details and indicators of compromise associated with LockBit ransomware operations.
The LockBit ransomware gang has been active since September 2019, in June 2021 the group announced the LockBit 2.0 RaaS. Like other ransomware gangs, Lockbit 2.0 determines the system and
user language settings and only targets those not matching a set list of languages that are
Eastern European.
After ransomware ads were banned on hacking forum, the LockBit operators set up their own leak site promoting the latest variant and advertising the LockBit 2.0 affiliate program.
“As infection begins, Lockbit 2.0 deletes log files and shadow copies residing on disk. Lockbit 2.0 enumerates system information to include hostname, host configuration, domain information, local drive configuration, remote shares, and mounted external storage devices. Lockbit 2.0 attempts to encrypt any data saved to any local or remote device but skips files associated with core system functions.” reads the flash alert. “Once completed, Lockbit 2.0 deletes itself from disk and creates persistence at startup. Prior to encryption, Lockbit affiliates primarily use the Stealbit application obtained directly from the Lockbit ransomware panel to exfiltrate specific file types.”
The LockBit Ransomware group is very active in this period, the list of victims is very long and includes Riviana, Accenture, Wormington & Bollinger, Anasia Group, Bangkok Airways, Italian energy company ERG, Vlastuin Group, E.M.I.T. Aviation Consulting, SCIS Air Security, Peabody Properties, DATA SPEED SRL, Island independent buying group, Ministry of Justice of France, Day Lewis, Buffington Law Firm and tens of other companies worldwide.
Ransomware operators have continuously improved their ransomware across the years by implementing new features, such as the support for Linux and VMware ESXi systems and the capability to abuse of group policies to encrypt Windows domains.
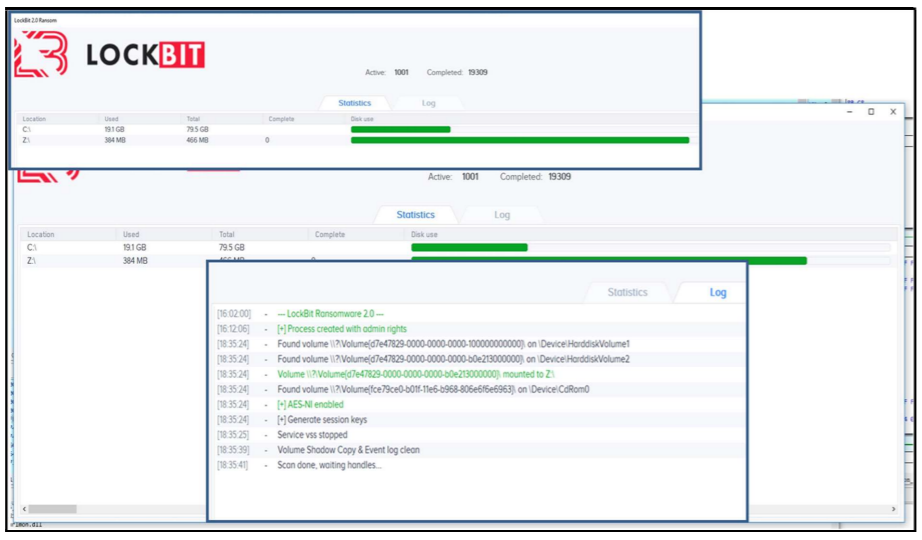
The flash alert details a Hidden debug / Status Window which can be activated by pressing Shift + F1 during the initial infection and provides real-time information on the process, status of user data destruction and encryption.
The FBI recommends victims avoid paying ransoms. The FBI is seeking any information about the Lockbit ransomware operations that can be shared, including boundary logs showing communication to and from foreign IP addresses, a sample ransom note, communications with the threat actors, Bitcoin wallet information, the decryptor file, and/or a benign sample of an encrypted file.
“The FBI encourages recipients of this document to report information concerning suspicious or criminal activity to their local FBI field office.” concludes the alert. “By reporting any related information to FBI Cyber Squads, you are assisting in sharing information that allows the FBI to track malicious actors and coordinate with private industry and the United States Government to prevent future intrusions and attacks.”
The FBI flash alert also includes mitigations to prevent LockBit ransomware infections:
- Require all accounts with password logins (e.g., service account, admin accounts, and domain admin accounts) to have strong, unique passwords
- Require multi-factor authentication for all services to the extent possible
- Keep all operating systems and software up to date
- Remove unnecessary access to administrative shares
- Use a host-based firewall to only allow connections to administrative shares via server message block (SMB) from a limited set of administrator machines.
- Enable protected files in the Windows Operating System to prevent unauthorized changes to critical files.
To limit an adversary from learning the organization’s enterprise environment, limit common system and network discovery techniques by taking the following actions:
- Segment networks to prevent the spread of ransomware
- Identify, detect, and investigate abnormal activity and potential traversal of the indicated ransomware with a networking monitoring tool
- Implement time-based access for accounts set at the admin level and higher
- Disable command-line and scripting activities and permissions
- Maintain offline backups of data, and regularly maintain backup and restoration
- Ensure all backup data is encrypted, immutable, and covers the entire organization’s data infrastructure
In January 2022 LockBit Ransomware hit European Firms & The French Ministry Of Justice, read more here LockBit ransomware hit European firms & French Ministry of Justice
Why not learn more about ransomware and how it works?
You may also enjoy reading, The largest DDoS to date, Microsoft mitigates a 3.47 Tbps DDoS attack
Stay informed of the latest Cybersecurity trends, threats and developments. Sign up for RiSec Weekly Cybersecurity Newsletter Today
Remember, CyberSecurity Starts With You!
- Globally, 30,000 websites are hacked daily.
- 64% of companies worldwide have experienced at least one form of a cyber attack.
- There were 20M breached records in March 2021.
- In 2020, ransomware cases grew by 150%.
- Email is responsible for around 94% of all malware.
- Every 39 seconds, there is a new attack somewhere on the web.
- An average of around 24,000 malicious mobile apps are blocked daily on the internet.