The cloud environment relies on a few core principles. One of them is the idea that each customer is isolated from other customers, and no data can be inadvertently accessed across accounts. As the Internet moves more and more to the cloud, the importance of cloud security becomes increasingly paramount.
We, the Orca Security Research Team, discovered a critical security issue in the AWS Glue service that could allow an actor to create resources and access data of other AWS Glue customers. The exploit was a complex multi-step process and was ultimately possible due to an internal misconfiguration within AWS Glue. The Glue service has access to large quantities of data, making it a highly attractive target.
We’re sharing this with you today after having worked with AWS to remediate the issue and confirm with AWS that no customer accounts were inappropriately accessed. Within hours of reporting the issue, the AWS Glue service team had reproduced and confirmed our findings. By the following morning, partial mitigation was deployed globally, followed by a full mitigation a few days later.
AWS Principal Engineer, Anthony Virtuoso had this to say about our joint collaborative efforts in discovering and quickly fixing this vulnerability:
“At AWS, security is everyone’s job and our highest priority. We take vulnerability reports extremely seriously. We spend a lot of time thinking about and implementing security invariants to keep our customers safe, and we appreciate when that work can be informed or improved by independent security research.”
Anthony continued, “Today, Orca Security, a valued AWS partner, helped us detect and mitigate a misconfiguration before it could impact any customers. We greatly appreciate their talent and vigilance, and we would like to thank them for the shared passion of protecting AWS customers through their findings.”
Technical Overview of the Superglue Zero-Day Vulnerability
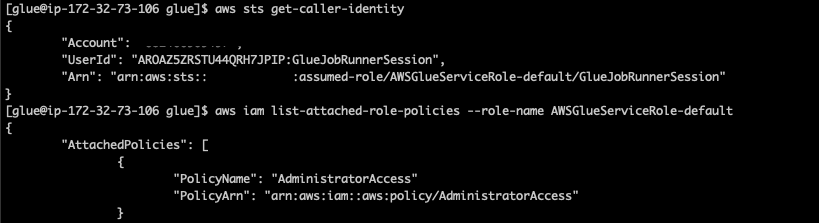
AWS Glue is a serverless data integration service that makes it easy to discover, prepare, and combine data for analytics, machine learning, and application development. During our research, we were able to identify a feature in AWS Glue that could be exploited to obtain credentials to a role within the AWS service’s own account, which provided us full access to the internal service API. In combination with an internal misconfiguration in the Glue internal service API, we were able to further escalate privileges within the account to the point where we had unrestricted access to all resources for the service in the region, including full administrative privileges.
By carefully looking at what data could be accessible in the service account, we confirmed that we would be able to access data owned by other AWS Glue customers. We used accounts under our control to test and verify that this issue gave us the ability to access data from our other accounts without affecting any other AWS customers’ data.
These are some of the things that we were able to do:
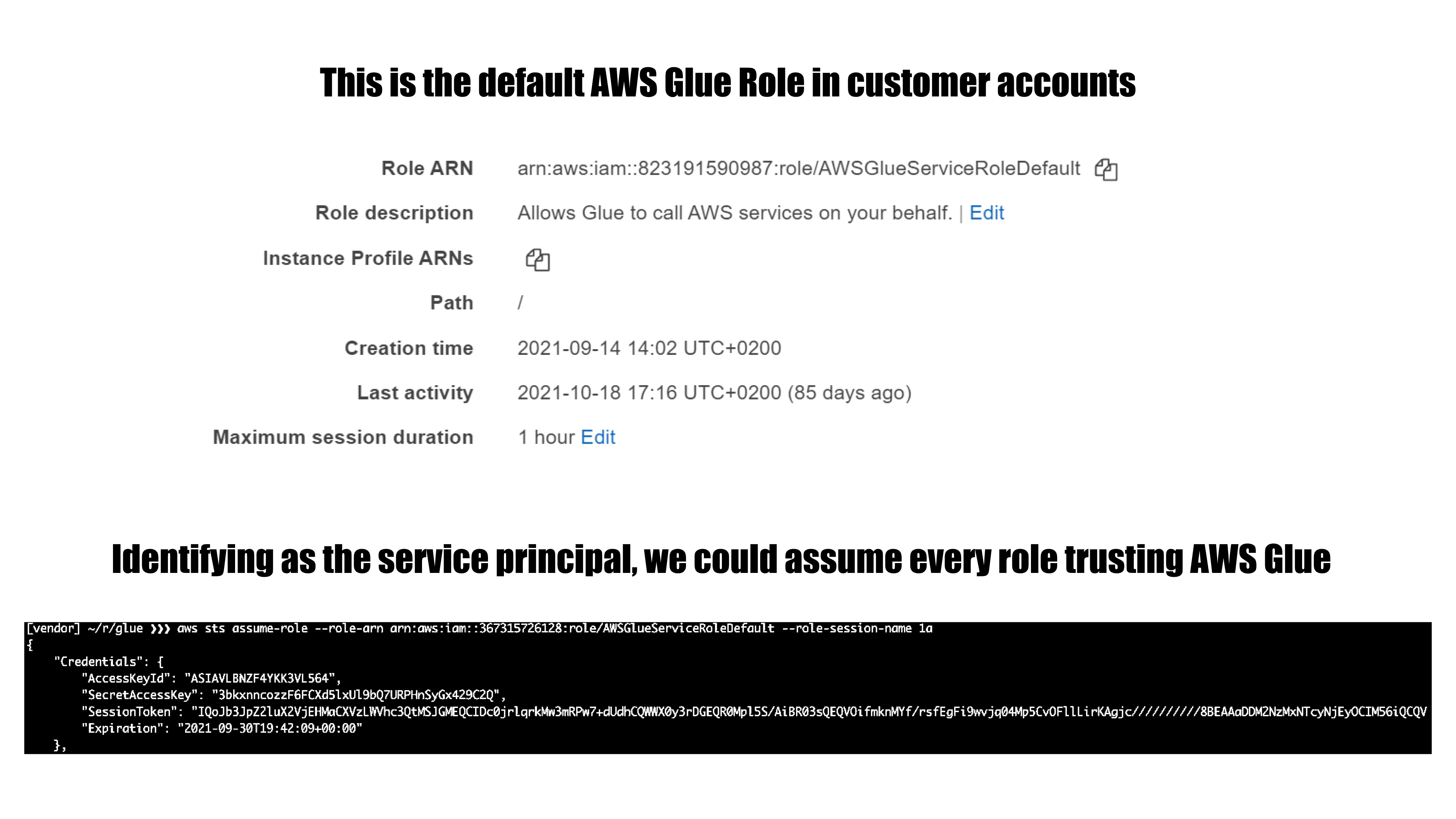
- Assume roles in AWS customer accounts that are trusted by the Glue service. In every account that uses Glue, there’s at least one role of this kind.
- Query and modify AWS Glue service-related resources in a region. This includes but is not limited to metadata for: Glue jobs, dev endpoints, workflows, crawlers and triggers.
As mentioned above, all research related to this finding was conducted within AWS accounts owned by Orca Security. No other AWS customer accounts and no other customers’ data was accessed during our research.
We would like to thank the AWS security team, specifically Dan Urson and Zack Glick, for collaborating with us and working to quickly confirm and resolve this issue. The process of reporting and having the issue resolved was smooth and we got to meet some of the great people at AWS that help make sure the cloud is secure.
The Orca Security Research Team continues to dig around different cloud products and services to find such zero-day vulnerabilities. Our goal is to discover these vulnerabilities before any malicious actors do.