The widely distributed FluBot malware continues to evolve, with new campaigns distributing the malware as Flash Player and the developers adding new features.
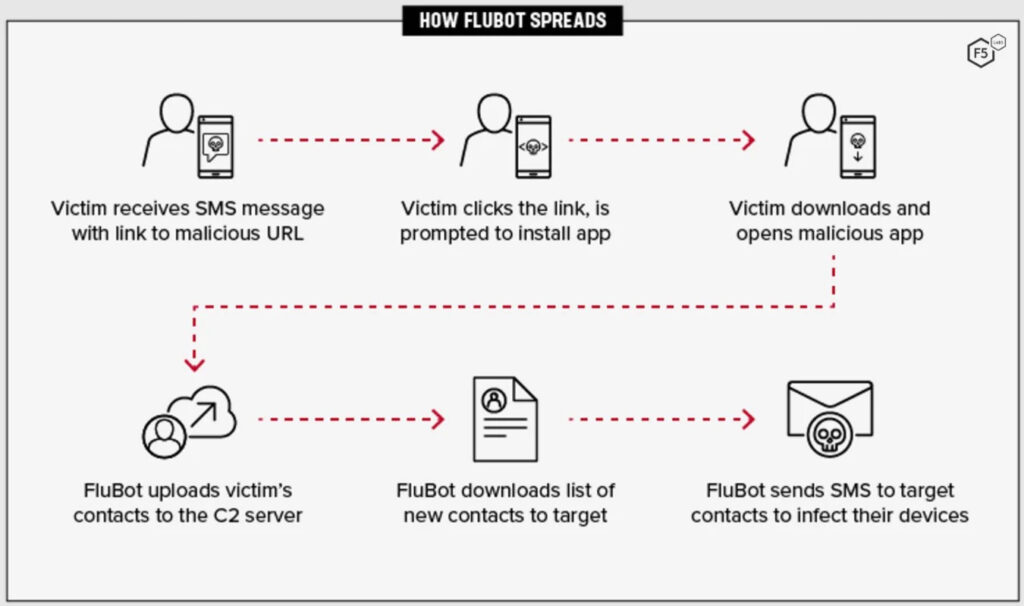
FluBot is an Android banking trojan that steals credentials by displaying overlay login forms against many banks worldwide.
The smishing (SMS phishing) lures for its distribution include fake security updates, fake Adobe Flash Players, voicemail memos, and impersonating parcel delivery notices.
Once in the device, FluBot can steal online banking credentials, send or intercept SMS messages (and one-time passwords), and capture screenshots.
Because the malware uses the victim’s device to send new smishing messages to all their contacts, it usually spreads like wildfire.
Source: F5 Labs
Impersonating Flash Player
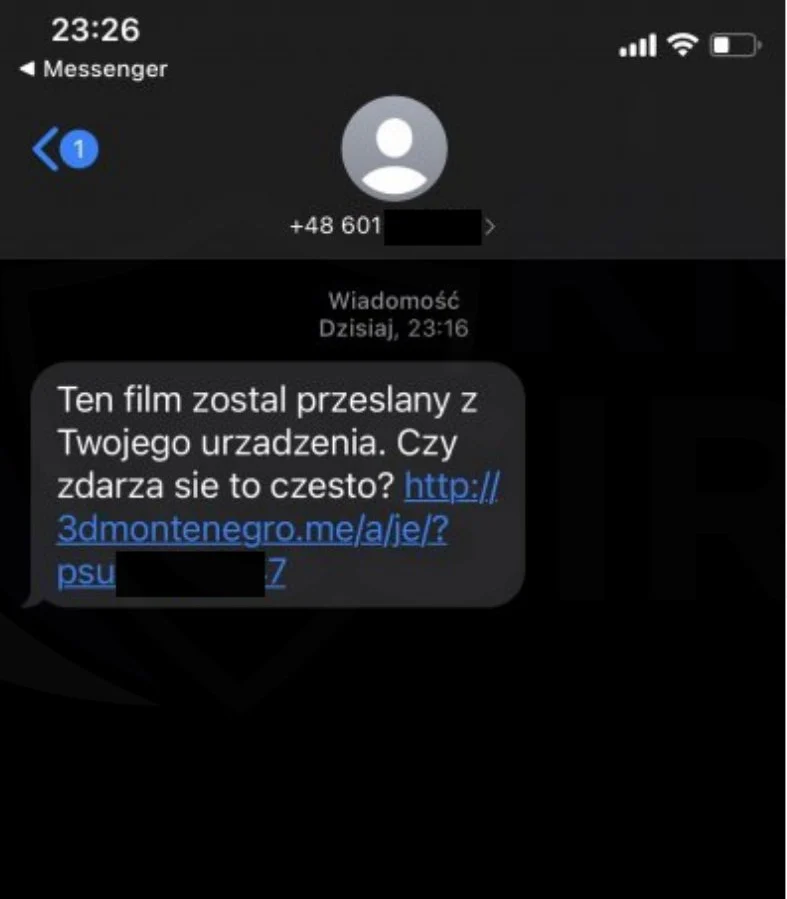
MalwareHunterTeam told BleepingComputer that new FluBot campaigns are distributed using SMS texts asking the recipient if they intended to upload a video from their device.
An example of this campaign’s SMS text targeting Polish recipients was shared by CSIRT KNF, as seen below.
Source: CSIRT KNF
When recipients click on the included link, they are brought to a page offering a fake Flash Player APK [VirusTotal] that installs the FluBot malware on the Android device.
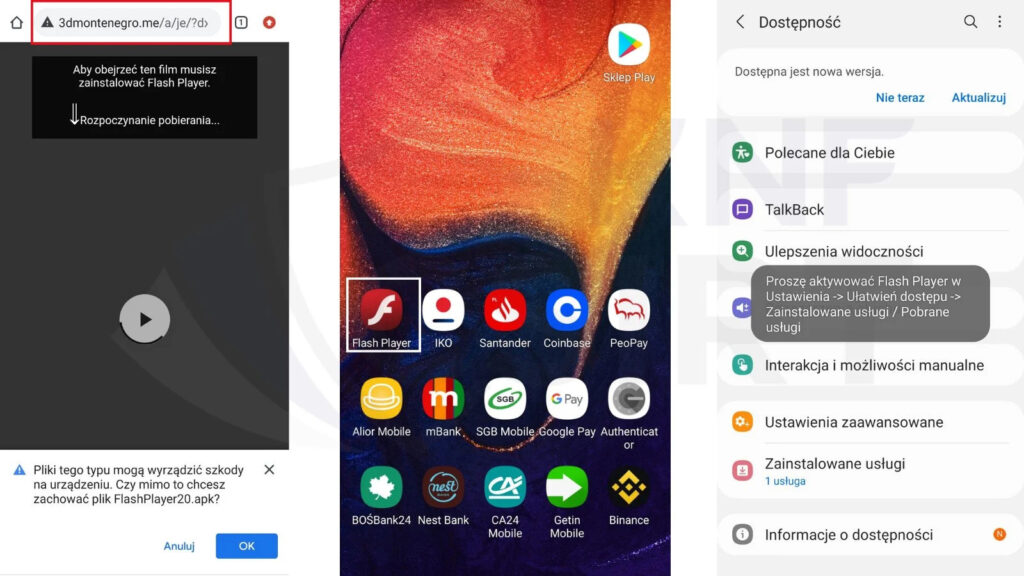
Source: CSIRT KNF
Android users should always avoid installing apps from APKs hosted at remote sites to protect themselves from malware. This practice is especially true for well-known brands, like Adobe, whose apps should only be installed from trusted locations.
New features observed in recent FluBot versions
The most recent major release is version 5.0, which came out in early December 2021, while version 5.2 saw the light only a few days ago.
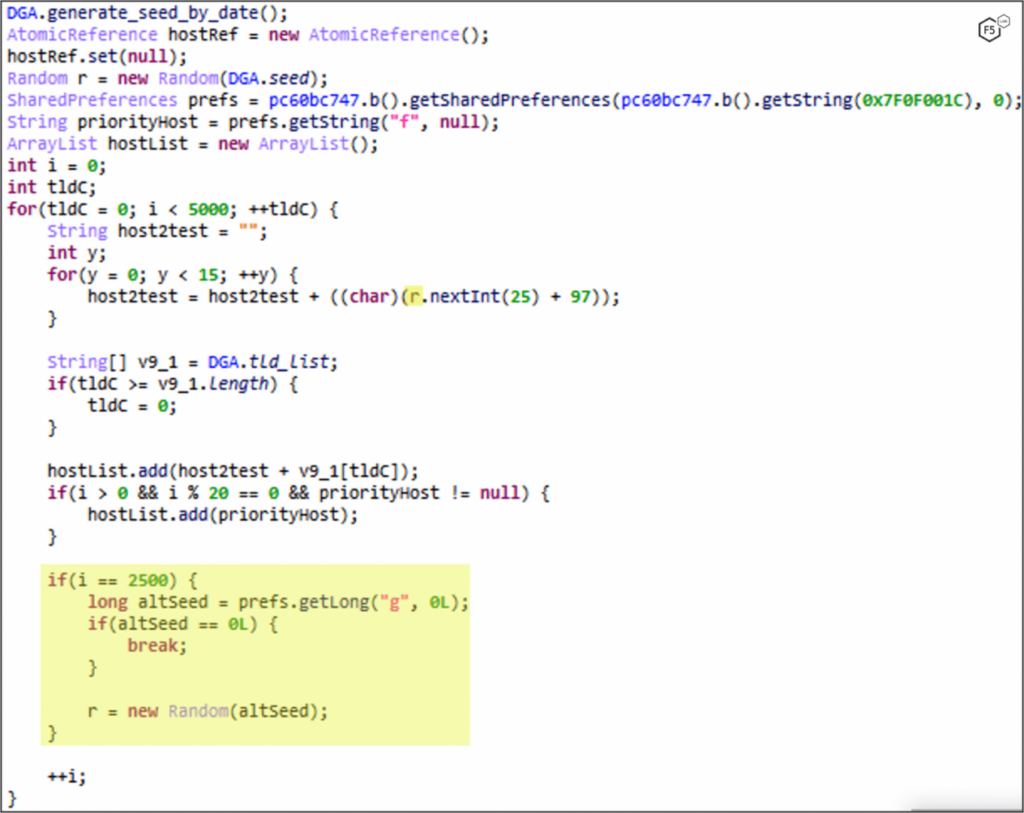
With this release, the DGA (domain generation algorithm) system received much attention from the malware authors, as it’s vital in enabling the actors to operate unobstructed.
DGA generates many new C2 domains on the fly, making mitigation measures such as DNS blocklists ineffective.
In its newest version, FluBot’s DGA uses 30 top-level domains instead of just three used previously and also features a command that enables attackers to change the seed remotely.
Source: F5 Labs
On the communication side, the new FluBot now connects to the C2 through DNS tunnelling over HTTPS, whereas previously, it used direct HTTPS port 443.
The commands added on the malware in versions 5.0, 5.1, and 5.2, are the following:
- Update DNS resolvers
- Update the DGA seed remotely
- Send longer SMS messages using multi-part division functions
Along with the above, the latest version of FluBot retains the capability to:
- Open URLs on demand
- Get the victim’s contact list
- Uninstall existing apps
- Disable Android Battery Optimization
- Abuse Android Accessibility Service for screen grabbing and keylogging
- Perform calls on demand
- Disable Play Protect
- Intercept and hide new SMS messages for stealing OTPs
- Upload SMS with victim information to C2
- Get list of apps to load the corresponding overlay injects
In summary, FluBot hasn’t deprecated any commands used in previous versions and only enriched its capabilities with new ones.
For more technical details on how exactly the latest version of FluBot works, check out the F5 Labs report.

How to stay safe from FluBot
Note that in many cases, a link to download FluBot will arrive on your device via one of your contacts, maybe even a friend or family.
As such, if you receive an unusual SMS that contains a URL and urges you to click it, it’s likely a message generated by FluBot.
Finally, avoid installing APK files from unusual sources, regularly check that Google Play Protect is enabled on your Android device, and use a mobile security solution from a reputable vendor.




