The often-exploited Remote Desktop Protocol (RDP) is once again in the news. This time, it has a new attack vector that was discovered by researchers and subsequently patched earlier this month by Microsoft.
Given that all versions of Windows for the past 10 years – for both desktop and server – need to be patched, you should put this on your priority list, especially since this new problem can be easily exploited.
RDP has a valuable function in today’s connectivity. It is used often as a way to provide remote access so that users don’t need to physically sit in front of their computers or servers. However, this utility has brought a dark past to the protocol and made RDP a security sinkhole. One of the more infamous attacks was called BlueKeep, which we covered when it happened in 2019. That was a full-on remote execution vulnerability that triggered warnings from the US National Security Agency for quick patching.
As a side note, the response to BlueKeep included help from Marcus Hutchins, who found a way to stop the WannaCry outbreak back in 2017. We also wrote how RDP is one of the more common ways that ransomware attacks can be launched and can also be used to initiate denial of service attacks.
In the latest incarnation of RDP exploits, hackers can gain access to data files using a man-in-the-middle attack across a Windows feature known as Named Pipes. This is a feature of Windows that was created more than 30 years ago to provide application-to-application communication that can connect processes on the same computer or across a network.
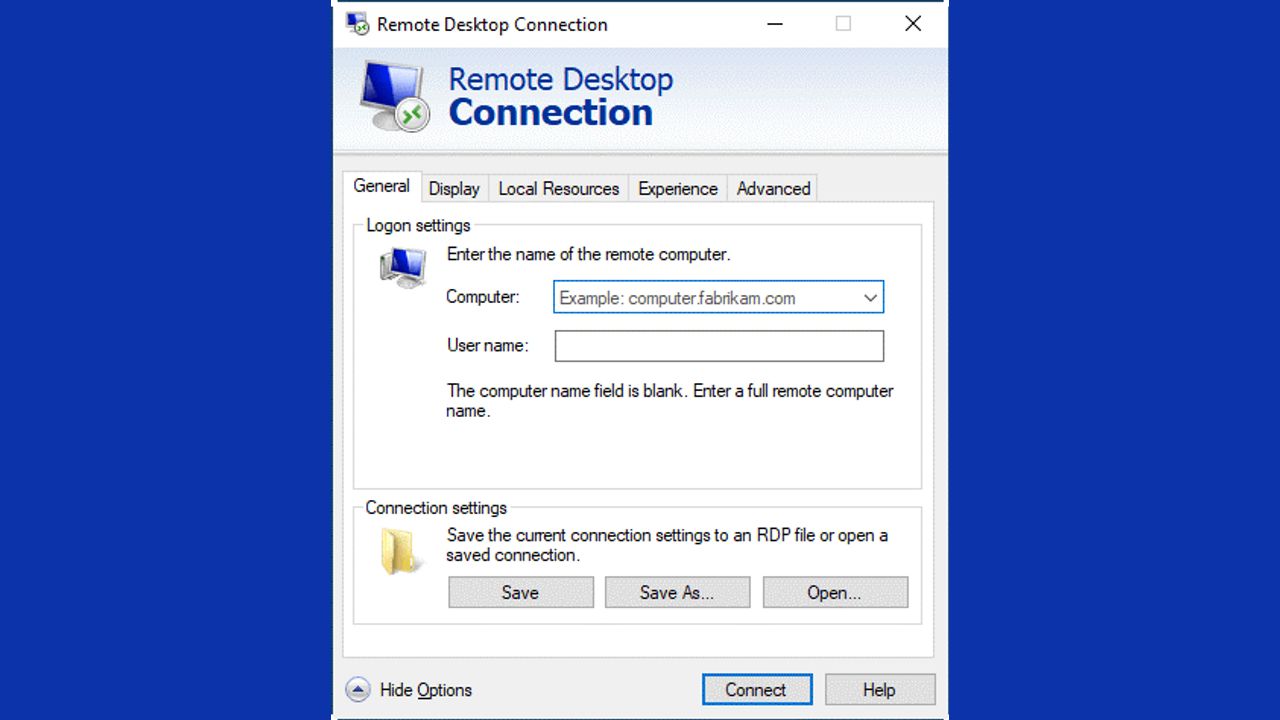
RDP needs to be implemented with care, as the protocol itself doesn’t have any inherent security features (such as the secure versions of Domain Name System or email protocols). Indeed, you might say that it has inherent insecurities, including:
- A well-known TCP/IP port (3389): Easy to track by hackers.
- Weak sign-in credentials: If users have a weak Windows login, hackers can use credential stuffing or brute force attacks to compromise this password.
- Numerous ways to exploit remote connections: The latest issue (Named Pipes) is merely one of many ways that attacks can worm their way into your systems. They can bring up “Show Options” or Help menus when first connecting to the remote gateway, both of which could allow for file directory browsing, or to bypass file execution block lists.
All of this makes for challenging implementations of RDP. Here are a few steps that you can take to secure its use:
1. Disable RDP when it isn’t needed. You should try this when you’re patching everything, as is suggested by Microsoft.
2. Use better passwords, especially on your local Windows equipment. Employ password managers and single-sign on tools. You have heard this advice before, no doubt, but it remains key!
3. Lock down port 3389, either through your network firewalls or other security tools. This can be tricky, because so many users might require remote access and all it would take to pull off an RDP exploit would be to compromise a single desktop.
4. Invest in better antivirus. Remote Access Shield is one of the features available in Avast Premium Security that can block RDP exploits.
5. Create more effective Active Directory group policies that block and allow specific applications and remote help options to be run remotely. Also, be sure to audit who has administrative privileges to ensure that the absolute minimum number of people have access.
You may also enjoy reading, The definitions of “recently” and “discovered” leave a lot to be desired
Stay informed of the latest Cybersecurity trends, threats and developments. Sign up for RiSec Weekly Cybersecurity Newsletter Today